Resource Library
Hang out and explore to learn more about everything from FileShares, Metadata, AI, and Information Governance


Shinydocs Blog
-1.jpg?width=2000&height=1125&name=Lets%20make%20a%20Podcast%20(EI)-1.jpg)
Enterprise Intelligence Podcast
Recent Webinars
How You Can Revolutionize Your Information Management Program, Like the Town of Milton
Hear from Jason Cassidy, CEO at Shinydocs, and get a practical guide to how municipalities can revolutionize their information management programs with Shinydocs Pro, plus a live product demo and a Q&A session.

Managing Content Sprawl and Achieving Legal Excellence in Law Firms
Watch Shinydocs and three expert panelists as we explore key topics on how law firm operations can enable high quality client services while navigating the complexities of risk and information governance.

Safeguard Your Client Data with iManage and Shinydocs Pro
See how Shinydocs Pro helps iManage customers efficiently protect client data and responsibly manage client files, within iManage, file shares, email, MS Teams, and more.
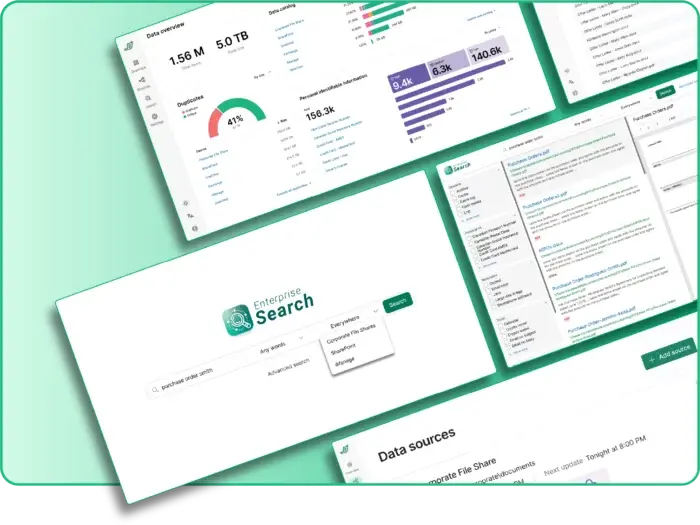
See Shinydocs Pro in Action
See how Shinydocs Pro automatically analyzes your content and gives you powerful and secure search across all your file shares and network drives. Then dive deeper into examples of classifying and reporting your content.
Ready to Automate your Document and File Analysis?
Chat with one of our knowledgeable specialists who can help you get started quickly and get immediate results.
